0. 背景
autojs是一个在Android编写、运行JavaScript代码的集成开发环境,包括代码补全的编辑器、单步调试、图形化设计,可构建为独立apk应用,也可连接电脑开发。
更新日志:参考 https://pro.autojs.org/docs/#/zh-cn/appChangeLog
autojs 4.1.1 alpha2: 为最后一个开源版本,不带加密功能。可以直接从https://github.com/hyb1996/Auto.js编译。
autojs pro 7: 带有离线加密和在线加密功能,但是已经不可以购买账号。autojs pro 7.0.4-1为最后一个版本。
autojs pro 8: 为目前比较新的版本,新增离线dex加密和snapshot加密两种加密方式,但是存在以下限制:
- 某些软件上自动点击等无障碍功能不能生效,目前包括主流社交软件、直播软件、短视频软件、淘宝等(这个列表可能会动态更新)
- 8.0不包含在线打包功能,以后可能考虑去掉离线加密功能。
autojs pro 8.7.5 离线dex加密
autojs pro 8.7.6 新增离线snapshot加密
autojs pro 9: 加密上无更新
1. encryptLevel为0(不加密)
方法一: frida hook解密
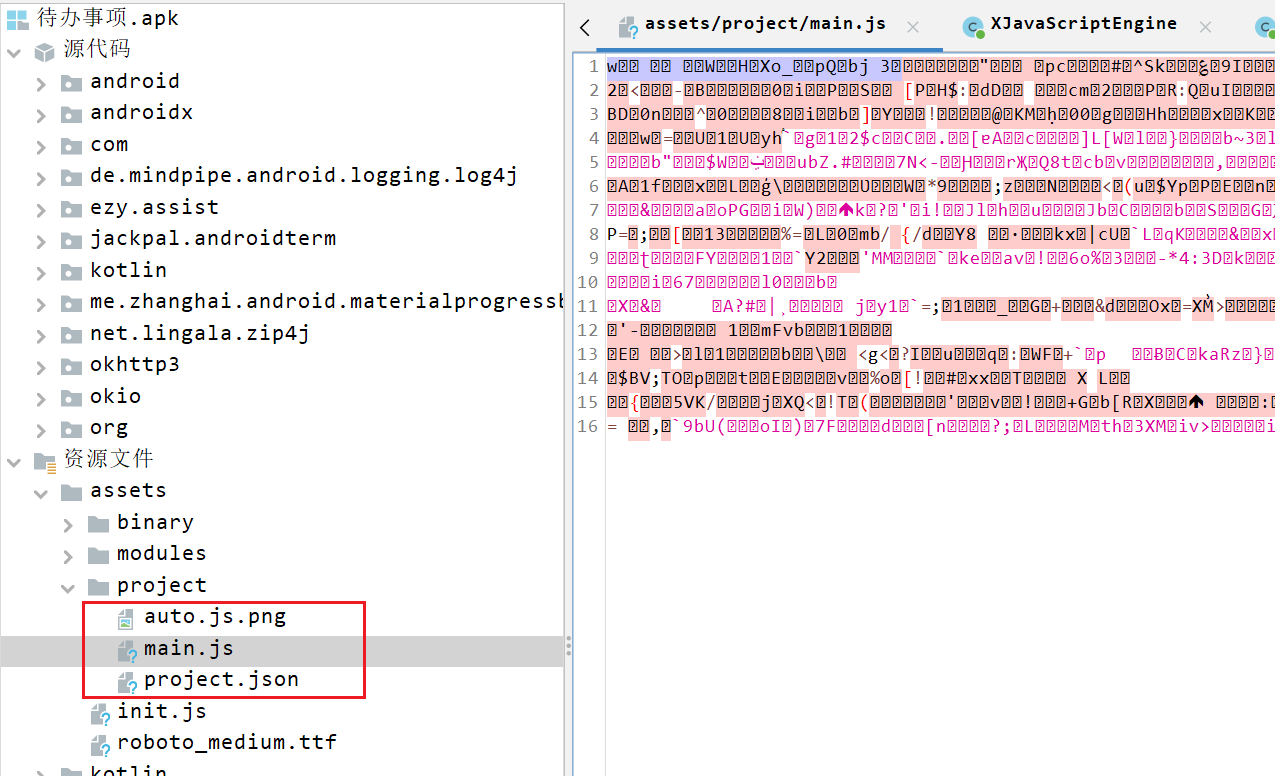
使用4.1.1版本,主动从实例中创建一个app样本,这里我打包了一个"代办事项"的apk,然后拖入jadx进行分析,在assets文件夹下面找到加密后的js和说明文件:
{
"assets": [],
"build": {
"build_id": "8E066D6B-1",
"build_number": 1,
"build_time": 1661513820823
},
"useFeatures": [],
"main": "main.js",
"name": "待办事项",
"packageName": "com.example.script1",
"scripts": {},
"versionCode": 1,
"versionName": "1.0.0"
}
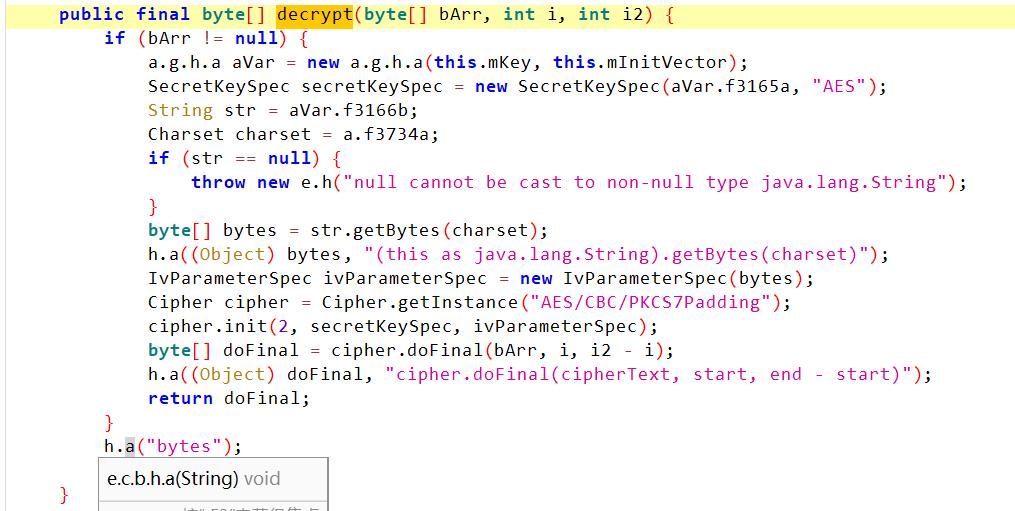
js源代码加了密码,直接查找decrypt等关键词,定位到以下函数:
接下来分析下这里是否能拿到解密后的js明文,采用frida进行函数调用的追踪:
function hook_class(className) {
Java.perform(function () {
Java.enumerateLoadedClasses({
onMatch: function (name) {
if (name.indexOf(className) != -1) {
traceClass(name)
}
},
onComplete: function () {
}
})
})
}
function printStack(name) {
Java.perform(function () {
var Exception = Java.use("java.lang.Exception");
var ins = Exception.$new("Exception");
var straces = ins.getStackTrace();
if (straces != undefined && straces != null) {
var strace = straces.toString();
var replaceStr = strace.replace(/,/g, "\n");
send("=============================" + name + " Stack start=======================");
send(replaceStr);
send("=============================" + name + " Stack end=======================\r\n");
Exception.$dispose();
}
});
}
function traceClass(clsname) {
try {
var target = Java.use(clsname);
var methods = target.class.getDeclaredMethods();
methods.forEach(function (method) {
var methodName = method.getName();
var overloads = target[methodName].overloads;
overloads.forEach(function (overload) {
var proto = "(";
overload.argumentTypes.forEach(function (type) {
proto += type.className + ", ";
});
if (proto.length > 1) {
proto = proto.substring(0, proto.length - 2);
}
proto += ")";
console.log("hooking: " + clsname + "." + methodName + proto);
overload.implementation = function () {
var args = [];
for (var j = 0; j < arguments.length; j++) {
args[j] = arguments[j] + ""
}
var retval = this[methodName].apply(this, arguments);
console.log(clsname + '.' + methodName + proto + " args: ", args, "ret:", retval)
printStack(clsname + '.' + methodName)
return retval;
}
});
});
} catch (e) {
send("'" + clsname + "' hook fail: " + e)
}
}
function main() {
hook_class("com.stardust.autojs.engine.encryption.ScriptEncryption")
}
setImmediate(main)
发现其在每次打开app的时候都会调用decrypt函数,将函数执行结果打印出来后,正好是js脚本。于是下面直接编写frida脚本拿解密结果即可。
index.js
function get_autojs_code() {
Java.perform(function () {
var clazz = Java.use("com.stardust.autojs.engine.encryption.ScriptEncryption");
clazz.decrypt.implementation = function (arg1, arg2, arg3) {
var result = this.decrypt(arg1, arg2, arg3);
send(utf8ByteToUnicodeStr(result))
return result;
}
})
}
function utf8ByteToUnicodeStr(utf8Bytes) {
var unicodeStr = "";
for (var pos = 0; pos < utf8Bytes.length;) {
var flag = utf8Bytes[pos];
var unicode = 0;
if ((flag >>> 7) === 0) {
unicodeStr += String.fromCharCode(utf8Bytes[pos]);
pos += 1;
} else if ((flag & 0xFC) === 0xFC) {
unicode = (utf8Bytes[pos] & 0x3) << 30;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 24;
unicode |= (utf8Bytes[pos + 2] & 0x3F) << 18;
unicode |= (utf8Bytes[pos + 3] & 0x3F) << 12;
unicode |= (utf8Bytes[pos + 4] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 5] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 6;
} else if ((flag & 0xF8) === 0xF8) {
unicode = (utf8Bytes[pos] & 0x7) << 24;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 18;
unicode |= (utf8Bytes[pos + 2] & 0x3F) << 12;
unicode |= (utf8Bytes[pos + 3] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 4] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 5;
} else if ((flag & 0xF0) === 0xF0) {
unicode = (utf8Bytes[pos] & 0xF) << 18;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 12;
unicode |= (utf8Bytes[pos + 2] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 3] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 4;
} else if ((flag & 0xE0) === 0xE0) {
unicode = (utf8Bytes[pos] & 0x1F) << 12;;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 2] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 3;
} else if ((flag & 0xC0) === 0xC0) { //110
unicode = (utf8Bytes[pos] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 1] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 2;
} else {
unicodeStr += String.fromCharCode(utf8Bytes[pos]);
pos += 1;
}
}
return unicodeStr;
}
index.py
## python 注入 frida js
import frida
import sys
target_app = "待办事项"
def on_message(message, data):
if message['type'] == 'send':
print("保存结果")
with open(f"{target_app}.js", 'w' ,encoding='utf-8') as f:
f.write(message["payload"])
else:
print(f"message: {message}")
jscode = open("index.js", encoding="utf-8").read()
device = frida.get_usb_device()
session = device.attach(target_app)
script = session.create_script(jscode)
script.on('message',on_message)
script.load()
sys.stdin.read()
方法二: 静态解密
通过frida hook分析的方式,可以看出js代码是采用了AES的方式进行的加解密,于是我们只需要找出iv和secret即可解密js。
下面尝试直接找出iv和secret,对所有的加解密函数进行hook:
var N_ENCRYPT_MODE = 1
var N_DECRYPT_MODE = 2
function showStacks() {
var Exception = Java.use("java.lang.Exception");
var ins = Exception.$new("Exception");
var straces = ins.getStackTrace();
if (undefined == straces || null == straces) {
return;
}
console.log("============================= Stack strat=======================");
console.log("");
for (var i = 0; i < straces.length; i++) {
var str = " " + straces[i].toString();
console.log(str);
}
console.log("");
console.log("============================= Stack end=======================\r\n");
Exception.$dispose();
}
//工具相关函数
var base64EncodeChars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/',
base64DecodeChars = new Array((-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), (-1), 62, (-1), (-1), (-1), 63, 52, 53, 54, 55, 56, 57, 58, 59, 60, 61, (-1), (-1), (-1), (-1), (-1), (-1), (-1), 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13, 14, 15, 16, 17, 18, 19, 20, 21, 22, 23, 24, 25, (-1), (-1), (-1), (-1), (-1), (-1), 26, 27, 28, 29, 30, 31, 32, 33, 34, 35, 36, 37, 38, 39, 40, 41, 42, 43, 44, 45, 46, 47, 48, 49, 50, 51, (-1), (-1), (-1), (-1), (-1));
function stringToBase64(e) {
var r, a, c, h, o, t;
for (c = e.length, a = 0, r = ''; a < c;) {
if (h = 255 & e.charCodeAt(a++), a == c) {
r += base64EncodeChars.charAt(h >> 2),
r += base64EncodeChars.charAt((3 & h) << 4),
r += '==';
break
}
if (o = e.charCodeAt(a++), a == c) {
r += base64EncodeChars.charAt(h >> 2),
r += base64EncodeChars.charAt((3 & h) << 4 | (240 & o) >> 4),
r += base64EncodeChars.charAt((15 & o) << 2),
r += '=';
break
}
t = e.charCodeAt(a++),
r += base64EncodeChars.charAt(h >> 2),
r += base64EncodeChars.charAt((3 & h) << 4 | (240 & o) >> 4),
r += base64EncodeChars.charAt((15 & o) << 2 | (192 & t) >> 6),
r += base64EncodeChars.charAt(63 & t)
}
return r
}
function base64ToString(e) {
var r, a, c, h, o, t, d;
for (t = e.length, o = 0, d = ''; o < t;) {
do
r = base64DecodeChars[255 & e.charCodeAt(o++)];
while (o < t && r == -1);
if (r == -1)
break;
do
a = base64DecodeChars[255 & e.charCodeAt(o++)];
while (o < t && a == -1);
if (a == -1)
break;
d += String.fromCharCode(r << 2 | (48 & a) >> 4);
do {
if (c = 255 & e.charCodeAt(o++), 61 == c)
return d;
c = base64DecodeChars[c]
} while (o < t && c == -1);
if (c == -1)
break;
d += String.fromCharCode((15 & a) << 4 | (60 & c) >> 2);
do {
if (h = 255 & e.charCodeAt(o++), 61 == h)
return d;
h = base64DecodeChars[h]
} while (o < t && h == -1);
if (h == -1)
break;
d += String.fromCharCode((3 & c) << 6 | h)
}
return d
}
function hexToBase64(str) {
return base64Encode(String.fromCharCode.apply(null, str.replace(/\r|\n/g, "").replace(/([\da-fA-F]{2}) ?/g, "0x$1 ").replace(/ +$/, "").split(" ")));
}
function base64ToHex(str) {
for (var i = 0, bin = base64Decode(str.replace(/[ \r\n]+$/, "")), hex = []; i < bin.length; ++i) {
var tmp = bin.charCodeAt(i).toString(16);
if (tmp.length === 1)
tmp = "0" + tmp;
hex[hex.length] = tmp;
}
return hex.join("");
}
function hexToBytes(str) {
var pos = 0;
var len = str.length;
if (len % 2 != 0) {
return null;
}
len /= 2;
var hexA = new Array();
for (var i = 0; i < len; i++) {
var s = str.substr(pos, 2);
var v = parseInt(s, 16);
hexA.push(v);
pos += 2;
}
return hexA;
}
function bytesToHex(arr) {
var str = '';
var k, j;
for (var i = 0; i < arr.length; i++) {
k = arr[i];
j = k;
if (k < 0) {
j = k + 256;
}
if (j < 16) {
str += "0";
}
str += j.toString(16);
}
return str;
}
function stringToHex(str) {
var val = "";
for (var i = 0; i < str.length; i++) {
if (val == "")
val = str.charCodeAt(i).toString(16);
else
val += str.charCodeAt(i).toString(16);
}
return val
}
function stringToBytes(str) {
var ch, st, re = [];
for (var i = 0; i < str.length; i++) {
ch = str.charCodeAt(i);
st = [];
do {
st.push(ch & 0xFF);
ch = ch >> 8;
}
while (ch);
re = re.concat(st.reverse());
}
return re;
}
//将byte[]转成String的方法
function bytesToString(utf8Bytes) {
var unicodeStr = "";
for (var pos = 0; pos < utf8Bytes.length;) {
var flag = utf8Bytes[pos];
var unicode = 0;
if ((flag >>> 7) === 0) {
unicodeStr += String.fromCharCode(utf8Bytes[pos]);
pos += 1;
} else if ((flag & 0xFC) === 0xFC) {
unicode = (utf8Bytes[pos] & 0x3) << 30;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 24;
unicode |= (utf8Bytes[pos + 2] & 0x3F) << 18;
unicode |= (utf8Bytes[pos + 3] & 0x3F) << 12;
unicode |= (utf8Bytes[pos + 4] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 5] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 6;
} else if ((flag & 0xF8) === 0xF8) {
unicode = (utf8Bytes[pos] & 0x7) << 24;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 18;
unicode |= (utf8Bytes[pos + 2] & 0x3F) << 12;
unicode |= (utf8Bytes[pos + 3] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 4] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 5;
} else if ((flag & 0xF0) === 0xF0) {
unicode = (utf8Bytes[pos] & 0xF) << 18;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 12;
unicode |= (utf8Bytes[pos + 2] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 3] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 4;
} else if ((flag & 0xE0) === 0xE0) {
unicode = (utf8Bytes[pos] & 0x1F) << 12;;
unicode |= (utf8Bytes[pos + 1] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 2] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 3;
} else if ((flag & 0xC0) === 0xC0) { //110
unicode = (utf8Bytes[pos] & 0x3F) << 6;
unicode |= (utf8Bytes[pos + 1] & 0x3F);
unicodeStr += String.fromCharCode(unicode);
pos += 2;
} else {
unicodeStr += String.fromCharCode(utf8Bytes[pos]);
pos += 1;
}
}
return unicodeStr;
}
function bytesToBase64(e) {
var r, a, c, h, o, t;
for (c = e.length, a = 0, r = ''; a < c;) {
if (h = 255 & e[a++], a == c) {
r += base64EncodeChars.charAt(h >> 2),
r += base64EncodeChars.charAt((3 & h) << 4),
r += '==';
break
}
if (o = e[a++], a == c) {
r += base64EncodeChars.charAt(h >> 2),
r += base64EncodeChars.charAt((3 & h) << 4 | (240 & o) >> 4),
r += base64EncodeChars.charAt((15 & o) << 2),
r += '=';
break
}
t = e[a++],
r += base64EncodeChars.charAt(h >> 2),
r += base64EncodeChars.charAt((3 & h) << 4 | (240 & o) >> 4),
r += base64EncodeChars.charAt((15 & o) << 2 | (192 & t) >> 6),
r += base64EncodeChars.charAt(63 & t)
}
return r
}
function base64ToBytes(e) {
var r, a, c, h, o, t, d;
for (t = e.length, o = 0, d = []; o < t;) {
do
r = base64DecodeChars[255 & e.charCodeAt(o++)];
while (o < t && r == -1);
if (r == -1)
break;
do
a = base64DecodeChars[255 & e.charCodeAt(o++)];
while (o < t && a == -1);
if (a == -1)
break;
d.push(r << 2 | (48 & a) >> 4);
do {
if (c = 255 & e.charCodeAt(o++), 61 == c)
return d;
c = base64DecodeChars[c]
} while (o < t && c == -1);
if (c == -1)
break;
d.push((15 & a) << 4 | (60 & c) >> 2);
do {
if (h = 255 & e.charCodeAt(o++), 61 == h)
return d;
h = base64DecodeChars[h]
} while (o < t && h == -1);
if (h == -1)
break;
d.push((3 & c) << 6 | h)
}
return d
}
//stringToBase64 stringToHex stringToBytes
//base64ToString base64ToHex base64ToBytes
// hexToBase64 hexToBytes
// bytesToBase64 bytesToHex bytesToString
Java.perform(function () {
var secretKeySpec = Java.use('javax.crypto.spec.SecretKeySpec');
secretKeySpec.$init.overload('[B', 'java.lang.String').implementation = function (a, b) {
showStacks();
var result = this.$init(a, b);
console.log("======================================");
console.log("算法名:" + b + "|str**:" + bytesToString(a));
console.log("算法名:" + b + "|Hex**:" + bytesToHex(a));
return result;
}
var DESKeySpec = Java.use('javax.crypto.spec.DESKeySpec');
DESKeySpec.$init.overload('[B').implementation = function (a) {
showStacks();
var result = this.$init(a);
console.log("======================================");
var bytes_key_des = this.getKey();
console.log("des** |str " + bytesToString(bytes_key_des));
console.log("des** |hex " + bytesToHex(bytes_key_des));
return result;
}
DESKeySpec.$init.overload('[B', 'int').implementation = function (a, b) {
showStacks();
var result = this.$init(a, b);
console.log("======================================");
var bytes_key_des = this.getKey();
console.log("des** |str " + bytesToString(bytes_key_des));
console.log("des** |hex " + bytesToHex(bytes_key_des));
return result;
}
var mac = Java.use('javax.crypto.Mac');
mac.getInstance.overload('java.lang.String').implementation = function (a) {
showStacks();
var result = this.getInstance(a);
console.log("======================================");
console.log("算法名:" + a);
return result;
}
mac.update.overload('[B').implementation = function (a) {
//showStacks();
this.update(a);
console.log("======================================");
console.log("update:" + bytesToString(a))
}
mac.update.overload('[B', 'int', 'int').implementation = function (a, b, c) {
//showStacks();
this.update(a, b, c)
console.log("======================================");
console.log("update:" + bytesToString(a) + "|" + b + "|" + c);
}
mac.doFinal.overload().implementation = function () {
//showStacks();
var result = this.doFinal();
console.log("======================================");
console.log("doFinal结果: |str :" + bytesToString(result));
console.log("doFinal结果: |hex :" + bytesToHex(result));
console.log("doFinal结果: |base64 :" + bytesToBase64(result));
return result;
}
mac.doFinal.overload('[B').implementation = function (a) {
//showStacks();
var result = this.doFinal(a);
console.log("======================================");
console.log("doFinal参数: |str :" + bytesToString(a));
console.log("doFinal结果: |str :" + bytesToString(result));
console.log("doFinal结果: |hex :" + bytesToHex(result));
console.log("doFinal结果: |base64 :" + bytesToBase64(result));
return result;
}
var md = Java.use('java.security.MessageDigest');
md.getInstance.overload('java.lang.String', 'java.lang.String').implementation = function (a, b) {
//showStacks();
console.log("======================================");
console.log("算法名:" + a);
return this.getInstance(a, b);
}
md.getInstance.overload('java.lang.String').implementation = function (a) {
//showStacks();
console.log("======================================");
console.log("算法名:" + a);
return this.getInstance(a);
}
md.update.overload('[B').implementation = function (a) {
//showStacks();
console.log("======================================");
console.log("update:" + bytesToString(a))
return this.update(a);
}
md.update.overload('[B', 'int', 'int').implementation = function (a, b, c) {
//showStacks();
console.log("======================================");
console.log("update:" + bytesToString(a) + "|" + b + "|" + c);
return this.update(a, b, c);
}
md.digest.overload().implementation = function () {
//showStacks();
console.log("======================================");
var result = this.digest();
console.log("digest结果:" + bytesToHex(result));
console.log("digest结果:" + bytesToBase64(result));
return result;
}
md.digest.overload('[B').implementation = function (a) {
//showStacks();
console.log("======================================");
console.log("digest参数:" + bytesToString(a));
var result = this.digest(a);
console.log("digest结果:" + bytesToHex(result));
console.log("digest结果:" + bytesToBase64(result));
return result;
}
var ivParameterSpec = Java.use('javax.crypto.spec.IvParameterSpec');
ivParameterSpec.$init.overload('[B').implementation = function (a) {
//showStacks();
var result = this.$init(a);
console.log("======================================");
console.log("iv向量: |str:" + bytesToString(a));
console.log("iv向量: |hex:" + bytesToHex(a));
return result;
}
var cipher = Java.use('javax.crypto.Cipher');
cipher.getInstance.overload('java.lang.String').implementation = function (a) {
//showStacks();
var result = this.getInstance(a);
console.log("======================================");
console.log("模式填充:" + a);
return result;
}
cipher.init.overload('int', 'java.security.Key').implementation = function (a, b) {
//showStacks();
var result = this.init(a, b);
console.log("======================================");
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
var bytes_key = b.getEncoded();
console.log("init key:" + "|str**:" + bytesToString(bytes_key));
console.log("init key:" + "|Hex**:" + bytesToHex(bytes_key));
return result;
}
cipher.init.overload('int', 'java.security.cert.Certificate').implementation = function (a, b) {
//showStacks();
var result = this.init(a, b);
console.log("======================================");
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
return result;
}
cipher.init.overload('int', 'java.security.Key', 'java.security.spec.AlgorithmParameterSpec').implementation = function (a, b, c) {
//showStacks();
var result = this.init(a, b, c);
console.log("======================================");
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
var bytes_key = b.getEncoded();
console.log("init key:" + "|str**:" + bytesToString(bytes_key));
console.log("init key:" + "|Hex**:" + bytesToHex(bytes_key));
return result;
}
cipher.init.overload('int', 'java.security.cert.Certificate', 'java.security.SecureRandom').implementation = function (a, b, c) {
//showStacks();
var result = this.init(a, b, c);
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
return result;
}
cipher.init.overload('int', 'java.security.Key', 'java.security.SecureRandom').implementation = function (a, b, c) {
//showStacks();
var result = this.init(a, b, c);
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
var bytes_key = b.getEncoded();
console.log("init key:" + "|str**:" + bytesToString(bytes_key));
console.log("init key:" + "|Hex**:" + bytesToHex(bytes_key));
return result;
}
cipher.init.overload('int', 'java.security.Key', 'java.security.AlgorithmParameters').implementation = function (a, b, c) {
//showStacks();
var result = this.init(a, b, c);
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
var bytes_key = b.getEncoded();
console.log("init key:" + "|str**:" + bytesToString(bytes_key));
console.log("init key:" + "|Hex**:" + bytesToHex(bytes_key));
return result;
}
cipher.init.overload('int', 'java.security.Key', 'java.security.AlgorithmParameters', 'java.security.SecureRandom').implementation = function (a, b, c, d) {
//showStacks();
var result = this.init(a, b, c, d);
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
var bytes_key = b.getEncoded();
console.log("init key:" + "|str**:" + bytesToString(bytes_key));
console.log("init key:" + "|Hex**:" + bytesToHex(bytes_key));
return result;
}
cipher.init.overload('int', 'java.security.Key', 'java.security.spec.AlgorithmParameterSpec', 'java.security.SecureRandom').implementation = function (a, b, c, d) {
//showStacks();
var result = this.update(a, b, c, d);
if (N_ENCRYPT_MODE == a)
{
console.log("init | 加密模式");
}
else if(N_DECRYPT_MODE == a)
{
console.log("init | 解密模式");
}
var bytes_key = b.getEncoded();
console.log("init key:" + "|str**:" + bytesToString(bytes_key));
console.log("init key:" + "|Hex**:" + bytesToHex(bytes_key));
return result;
}
cipher.update.overload('[B').implementation = function (a) {
//showStacks();
var result = this.update(a);
console.log("======================================");
console.log("update:" + bytesToString(a));
return result;
}
cipher.update.overload('[B', 'int', 'int').implementation = function (a, b, c) {
//showStacks();
var result = this.update(a, b, c);
console.log("======================================");
console.log("update:" + bytesToString(a) + "|" + b + "|" + c);
return result;
}
cipher.doFinal.overload().implementation = function () {
//showStacks();
var result = this.doFinal();
console.log("======================================");
console.log("doFinal结果: |str :" + bytesToString(result));
console.log("doFinal结果: |hex :" + bytesToHex(result));
console.log("doFinal结果: |base64 :" + bytesToBase64(result));
return result;
}
cipher.doFinal.overload('[B').implementation = function (a) {
//showStacks();
var result = this.doFinal(a);
console.log("======================================");
console.log("doFinal参数: |str :" + bytesToString(a));
console.log("doFinal结果: |str :" + bytesToString(result));
console.log("doFinal结果: |hex :" + bytesToHex(result));
console.log("doFinal结果: |base64 :" + bytesToBase64(result));
return result;
}
var x509EncodedKeySpec = Java.use('java.security.spec.X509EncodedKeySpec');
x509EncodedKeySpec.$init.overload('[B').implementation = function (a) {
//showStacks();
var result = this.$init(a);
console.log("======================================");
console.log("RSA**:" + bytesToBase64(a));
return result;
}
var rSAPublicKeySpec = Java.use('java.security.spec.RSAPublicKeySpec');
rSAPublicKeySpec.$init.overload('java.math.BigInteger', 'java.math.BigInteger').implementation = function (a, b) {
//showStacks();
var result = this.$init(a, b);
console.log("======================================");
//console.log("RSA**:" + bytesToBase64(a));
console.log("RSA**N:" + a.toString(16));
console.log("RSA**E:" + b.toString(16));
return result;
}
var KeyPairGenerator = Java.use('java.security.KeyPairGenerator');
KeyPairGenerator.generateKeyPair.implementation = function ()
{
//showStacks();
var result = this.generateKeyPair();
console.log("======================================");
var str_private = result.getPrivate().getEncoded();
var str_public = result.getPublic().getEncoded();
console.log("公钥 |hex" + bytesToHex(str_public));
console.log("私钥 |hex" + bytesToHex(str_private));
return result;
}
KeyPairGenerator.genKeyPair.implementation = function ()
{
//showStacks();
var result = this.genKeyPair();
console.log("======================================");
var str_private = result.getPrivate().getEncoded();
var str_public = result.getPublic().getEncoded();
console.log("公钥 |hex" + bytesToHex(str_public));
console.log("私钥 |hex" + bytesToHex(str_private));
return result;
}
});
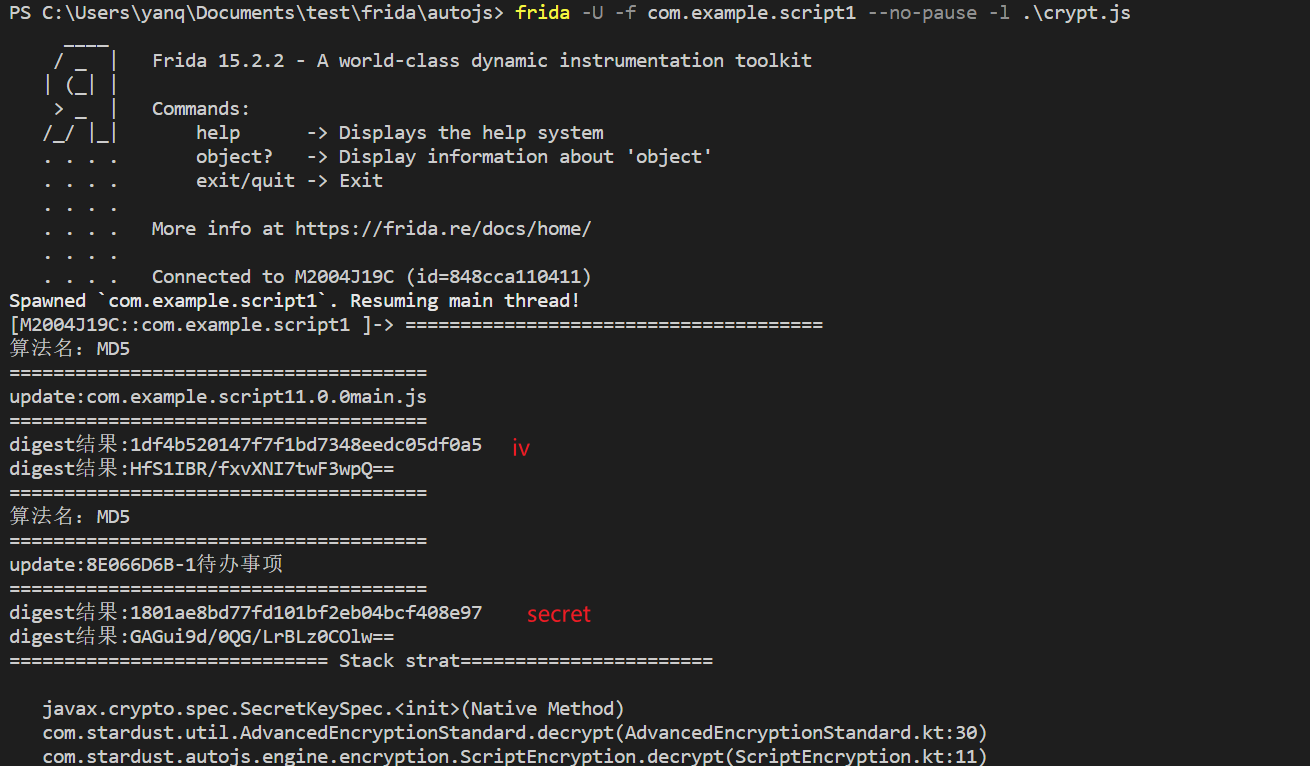
再结合
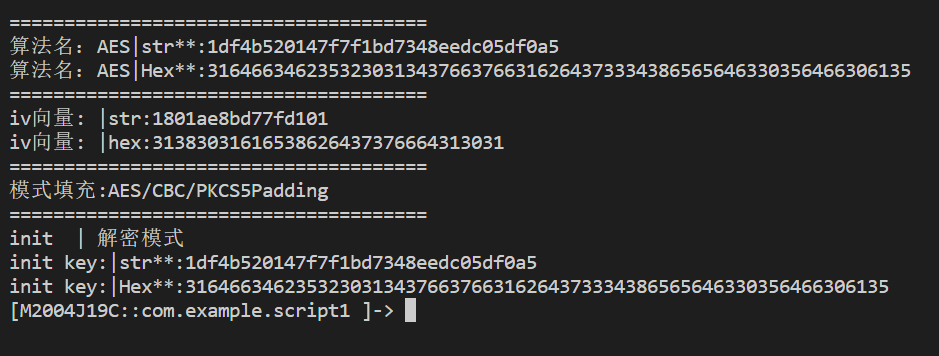
可以看出解密方式为:
AES/CBC/PKCS5Padding
key = MD5(packageName + versionName + main)
iv= MD5(build_id + name)前16位
编写出解密脚本为
from apkutils import APK
import zipfile
import sys
import json
from Crypto.Cipher import AES
from base64 import b64decode, b64encode
import hashlib
class AESCipher:
def __init__(self, secretkey: bytes, iv:bytes):
self.key = secretkey # 密钥
self.iv = iv # 偏移量
def pk5_decrypt(self, encrypted_text:bytes):
"""
解密: aes解密
:param encrypted_text : 已经加密的密文
:return:
"""
cipher = AES.new(key=self.key, mode=AES.MODE_CBC, IV=self.iv)
decrypted_text = cipher.decrypt(encrypted_text)
# 去除补位
unpad = lambda s: s[:-ord(s[-1:])]
return unpad(decrypted_text).decode('utf-8')
if __name__=="__main__":
# apk = APK.from_file()
zipfiles = zipfile.ZipFile("待办事项.apk")
config = json.load(zipfiles.open("assets/project/project.json"))
print(f"读取到project.json:{config}")
build_id = config["build"]["build_id"]
main = config["main"]
package_name = config["packageName"]
version_name = config["versionName"]
name = config["name"]
key = hashlib.md5(f"{package_name}{version_name}{main}".encode(encoding='UTF-8')).hexdigest() # MD5(packageName + versionName + main)
key = key.encode()
iv = hashlib.md5(f"{build_id}{name}".encode(encoding='UTF-8')).hexdigest()[:16] # MD5(build_id + name)前16位
iv = iv.encode()
print(f"key({type(key)}):{key}")
print(f"iv:({type(iv)}):{iv}")
aes = AESCipher(key, iv)
namelist = zipfiles.namelist() # 得到压缩包里所有文件
print(f"下面解析apk的assets/project/文件")
for name in namelist:
if "assets/project/" in name and name.endswith(".js"):
print(f"解密到{name}")
data = zipfiles.open(name).read()
decrypted_text = aes.pk5_decrypt(data[8:]) # 解密
# print(decrypted_text)
2. encryptLevel为1
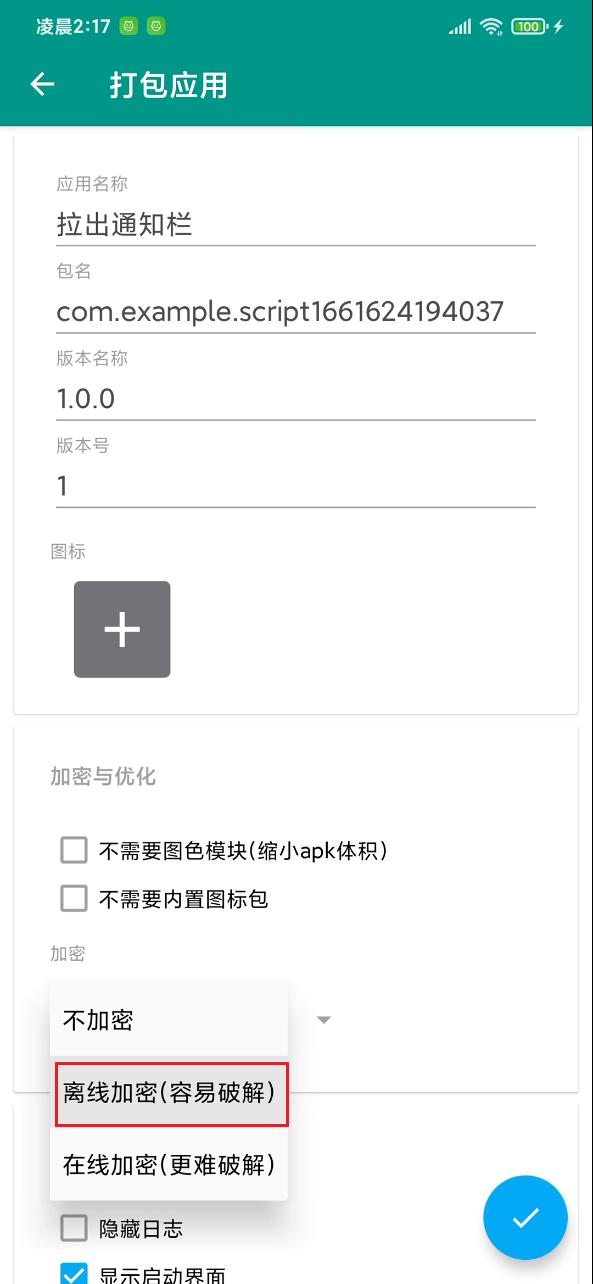
上面的情况是打包时没有选择加密的情况,下面测试加密的情况。通过autojs pro 7.0.4-1版本的autojs pro打包出一个新的app,选用了离线加密。
打开project.json如下:
{
"assets": [],
"build": {
"build_id": "39DB2720-1",
"build_number": 1,
"build_time": 1661624286327,
"release": true
},
"encryptLevel": 1,
"useFeatures": [],
"launchConfig": {
"displaySplash": true,
"hideLogs": false,
"splashText": "Powered by Auto.js Pro",
"stableMode": false
},
"main": "main.js",
"name": "拉出通知栏",
"optimization": {
"removeOpenCv": false,
"unusedResources": false
},
"packageName": "com.example.script1661624194037",
"scripts": {},
"versionCode": 1,
"versionName": "1.0.0"
}
可以看到encryptLevel为1,下面进行解密分析。
方法一: frida hook解密
分析后发现,和encryptLevel为0的hook方式一致,略。
方法二: 静态解密
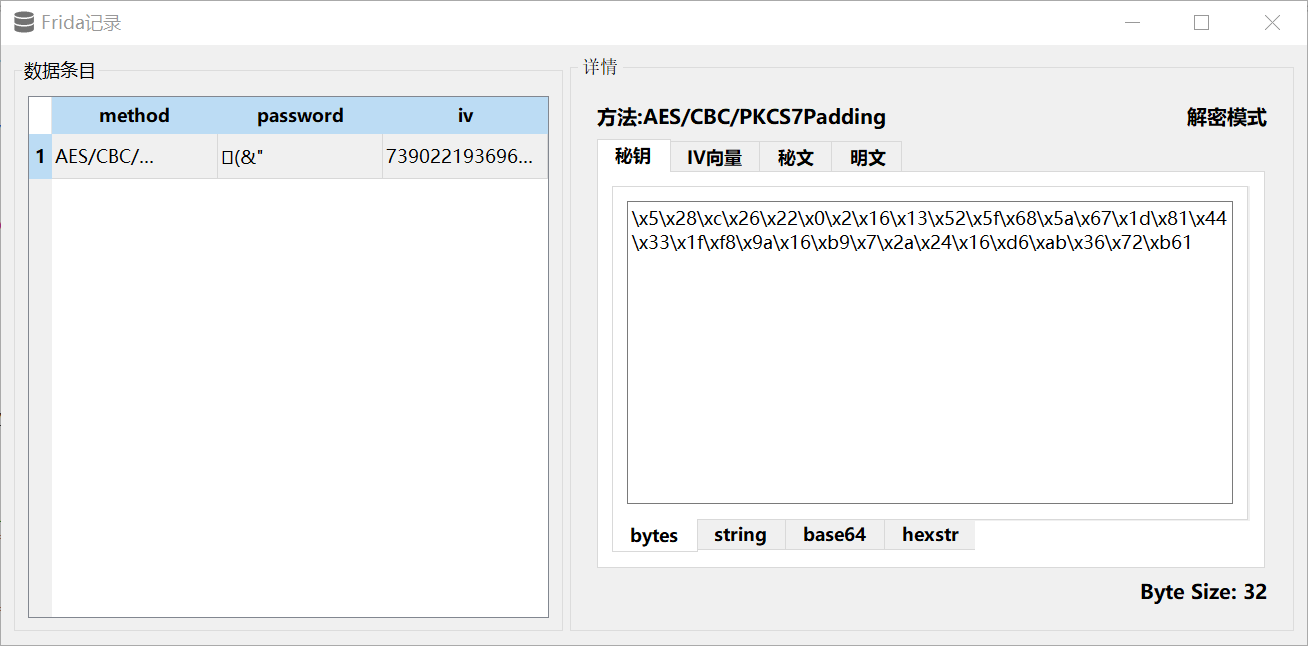
还是通过trace所有aes加密函数的方式进行分析。发现密钥key变了,变成了一段乱码:
于是静态分析发现以下代码:
com.stardust.autojs.engine.encryption.initFingerprint(ProjectConfig projectConfig)
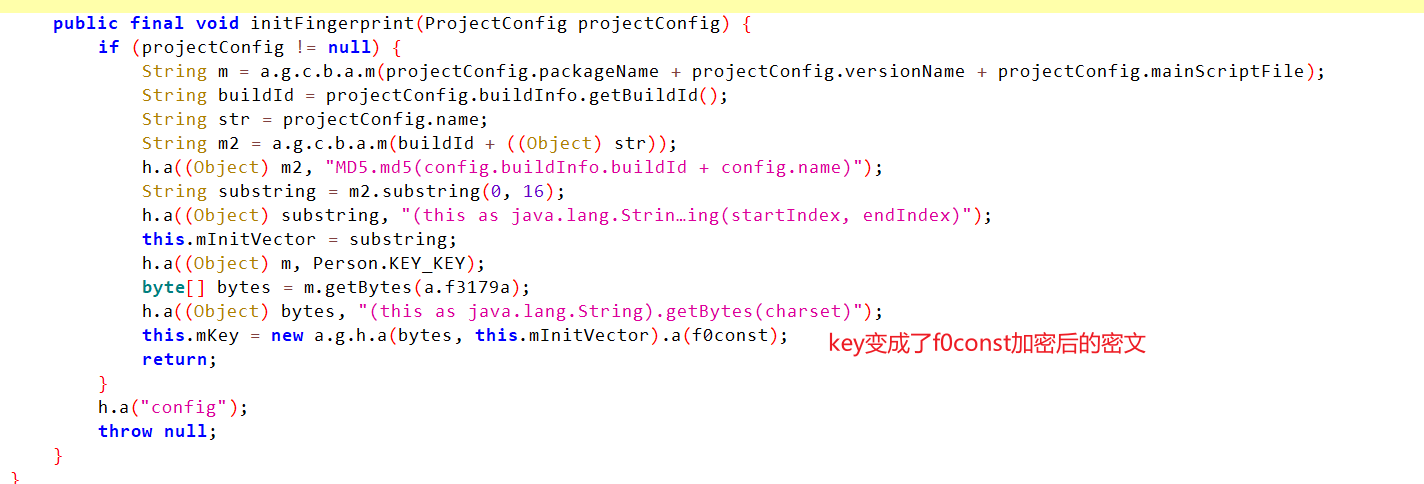
得出以下解密方式
AES/CBC/PKCS7Padding
iv= MD5(build_id + name)前16位
key = MD5(packageName + versionName + main)
然后通过iv和key加密一段字符串,密文为key2
然后通过iv和key2,即可解密js脚本。
3. encryptLevel为2、3
待分析
encryptLevel=3为snapshot加密,解密比较麻烦。
4. 通用脚本
针对encryptLevel为1以下的,通用的离线解密js脚本: https://github.com/saucer-man/autojs_reverse
